Pentesting as a Service for Teams That Ship Fast
Get continuous security assurance without the cost of building an internal pentesting team.
Traditional pentesting delivers a report.
Building an in-house offensive security team takes months and a lot of money.
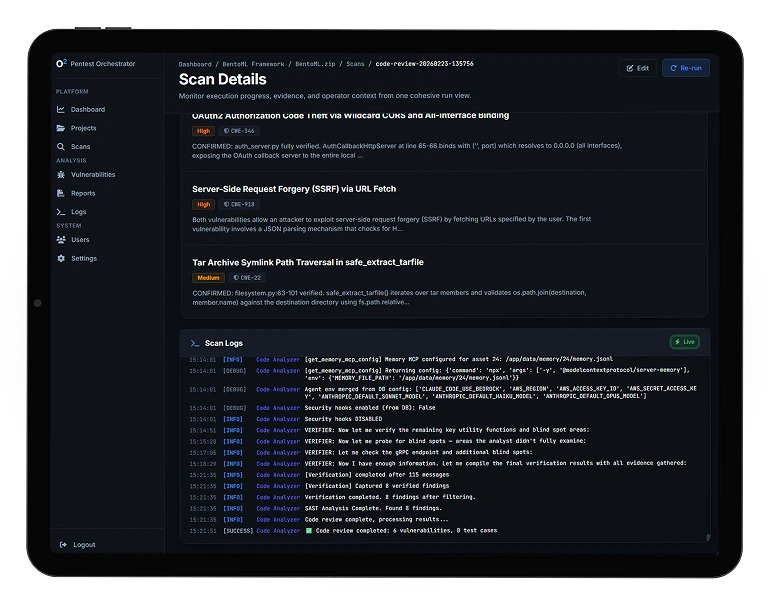
we45 PTaaS gives you expert pentesters and AI-assisted orchestration that reduce the time between vulnerability discovery and verified remediation, helping teams meet compliance deadlines faster while avoiding the cost of building an internal pentesting capability.

.svg)













.png)