Build real security skills with AppSecEngineer—50% off sitewide with code 'NOEXCUSES50'.

The landscape of cybersecurity in 2026 has been defined by an aggressive shift toward upstream supply chain exploitation, where the compromise of a single trusted utility can cascade into a global security crisis. On March 31, 2026, the JavaScript ecosystem encountered one of its most significant threats to date with the discovery of a sophisticated, cross-platform Remote Access Trojan (RAT) distributed through the widely used Axios HTTP client library. This incident, characterized by the injection of a malicious dependency named plain-crypto-js, represents a watershed moment in the weaponization of open-source registries. With Axios serving as a fundamental building block for modern web applications and boasting over 100 million weekly downloads, the reach of this compromise is practically unparalleled in the history of npm-based malware.
The breach was not a spontaneous event but a meticulously planned operation involving pre-staged decoy packages, the bypass of established security protocols like OIDC Trusted Publishing, and the deployment of multi-stage payloads tailored for macOS, Windows, and Linux environments. This report provides an exhaustive technical analysis of the Axios supply chain attack, detailing the timeline of events, the mechanism of the account takeover, the intricate obfuscation techniques within the plain-crypto-js dropper, and the broader implications for enterprise security architectures in an era of AI-driven cyber warfare.
To understand the gravity of the March 2026 breach, one must first examine the role of Axios within the global software development lifecycle. Axios is a promise-based HTTP client for the browser and node.js, providing a unified interface for making network requests. Its simplicity, reliability, and extensive feature set have made it the de facto standard for developers across all sectors, from finance and healthcare to government and artificial intelligence research.
As of early 2026, Axios is classified as a "Key Ecosystem Project" by major security analysis platforms, reflecting its critical position in the supply chain. The library's popularity is not merely a matter of developer preference but a structural reality of modern computing, where thousands of other packages and frameworks depend on Axios as a transitive dependency.
.png)
The sheer volume of downloads—exceeding 100 million per week—means that any malicious version published to the npm registry has the potential to infect millions of systems within hours. Automated CI/CD pipelines, which often pull the latest "patch" versions of dependencies to ensure security and stability, became the primary conduits for the spread of the plain-crypto-js Trojan.
The Axios supply chain attack was characterized by an 18-hour pre-staging phase designed to deceive reputation-based security scanners. By establishing a seemingly legitimate history for the malicious dependency, the attacker minimized the "new package" alarms that typically trigger during supply chain audits.
The timeline began on March 30, 2026, when the attacker utilized a throwaway npm account, nrwise, to seed the infrastructure. This account, linked to a ProtonMail address (nrwise@proton.me), was used to publish a clean version of plain-crypto-js that contained no malicious code. This decoy version (4.2.0) was a verbatim copy of the legitimate crypto-js library, ensuring that any initial inspection would find nothing suspicious.
.png)
Registry Response: Malicious packages removed by npm security.
All affected versions
The attack moved into its active phase at 23:59 UTC on March 30, when version 4.2.1 of plain-crypto-js was released. This version introduced the setup.js dropper and a postinstall lifecycle hook in the package.json manifest. Within minutes, the attacker leveraged a compromised maintainer account to publish two malicious versions of Axios—1.14.1 for the modern branch and 0.30.4 for the legacy branch—ensuring maximum coverage across both current and older enterprise projects.
The most significant technical failure highlighted by the Axios breach was the bypass of npm's Trusted Publishing mechanism. In a move to harden the supply chain, the Axios project had previously implemented OpenID Connect (OIDC) to cryptographically link package releases to verified GitHub Actions workflows. Under normal circumstances, this system ensures that only code generated within a specific, transparent CI environment can be published to the registry, effectively neutralizing the risk of stolen long-lived developer tokens.
However, the analysis of the malicious axios@1.14.1 release revealed a total breakdown of this chain of trust. The attacker gained access to the jasonsaayman npm account, a primary maintainer of Axios, and immediately changed the registered email to ifstap@proton.me. Evidence suggests the attacker obtained a "classic" npm access token that was not bound by OIDC constraints. This allowed the adversary to manually publish the poisoned packages directly from a local machine via the npm CLI, bypassing the project's official GitHub repository and automated pipelines entirely.
A forensic comparison of the metadata for the legitimate and malicious versions provides a clear signature of the compromise. Legitimate releases are published by the GitHub Actions user with an OIDC configuration ID, whereas the malicious release was published by the compromised maintainer's account with no provenance information.
.png)
The absence of a gitHead in the malicious version is particularly telling, as it confirms that the release has no corresponding commit in the official Axios GitHub repository. This discrepancy is a critical forensic signal for developers and automated scanners to identify packages that have been published outside of a verified development process.
The plain-crypto-js@4.2.1 package serves as the primary infection vector, utilizing a postinstall script to execute the setup.js dropper immediately upon installation. The script is heavily obfuscated to evade static analysis tools and manual inspection.
The obfuscation strategy relies on a two-layer decoding mechanism. All sensitive strings—including module names like child_process, file paths, and the Command and Control (C2) URL—are stored in a large, encoded array named stq. Two functions, _trans_1(x, r) (an XOR cipher) and a secondary translation routine, are used to reconstruct the plaintext at runtime.
The dropper dynamically loads the necessary Node.js modules, such as fs, os, and child_process, to minimize the footprint of the initial script. By using execSync for shell command execution, the malware can launch system-level processes without triggering the asynchronous event loops that some monitoring tools track.
The entry point of the malicious logic is a function call _entry("6202033"), where the string "6202033" acts as both a campaign identifier and a dynamic path for the C2 infrastructure.1 The script identifies the host operating system through the os.platform() method and branches into three distinct payload delivery paths.
.png)
The choice of these paths demonstrates a high degree of operational security awareness. On macOS, the path /Library/Caches/com.apple.act.mond mimics legitimate Apple system daemons (Activity Monitor), making it less likely to be flagged by casual inspection of running processes. On Windows, the use of %PROGRAMDATA% provides a stable location for persistence that survives system reboots and is often excluded from aggressive user-level cleanup scripts.
The true danger of the Axios compromise lies in the second-stage Remote Access Trojan (RAT) payloads, which are tailored to exploit the native capabilities of each target platform. The dropper contacts a live C2 server to retrieve these payloads, using specific identifiers to request the correct binary.
On Windows systems, the attack follows a multi-step sequence designed to leverage legitimate system binaries—a technique often referred to as "Living off the Land" (LotL).
The macOS payload delivery utilizes osascript to run AppleScript commands that fetch a second-stage RAT binary. The binary is placed in a system-level cache directory, granted execution permissions via chmod 770, and launched in the background through /bin/zsh.
For Linux environments, the dropper assumes the presence of curl and python. It fetches a Python-based RAT script to /tmp/ld.py and executes it using the nohup command. This ensures that the malware detaches from the parent process (the npm installation) and continues to run even after the developer closes their terminal session.
The command and control infrastructure for the Axios attack was hosted on the domain sfrclak.com, resolving to the IP address 142.11.206.73. The server operated on port 8000 and utilized a specific pathing structure to differentiate between the various stages and targets of the campaign.
A sophisticated aspect of the C2 communication was the attempt to blend into benign network traffic. When the dropper requested the second-stage payloads, it sent a POST body containing the string packages.npm.org/product followed by a platform-specific ID (e.g., product1 for Windows). This technique is designed to deceive network defenders and automated SIEM rules that might flag connections to unknown IPs but ignore traffic that appears to be related to legitimate npm registry communication.
.png)
The ultimate goal of the RAT is the large-scale exfiltration of high-value credentials and secrets. Given that Axios is frequently used in cloud-native and server-side environments, the infected machines likely hold extensive administrative access to production infrastructure. The RAT is configured to scan for and exfiltrate:
The authors of the plain-crypto-js malware implemented a rigorous forensic evasion protocol to conceal the breach from post-mortem analysis. Once the second-stage RAT is successfully launched and persistence is established, the setup.js script initiates a three-step self-destruction sequence.
First, the script uses the Node.js fs.unlink() method to delete itself (setup.js) from the local file system. Second, it deletes the original package.json file that contained the incriminating postinstall hook. Finally, it renames a pre-staged file, package.md, to package.json.
This "clean" version of package.json identifies the package as version 4.2.0 and contains no references to any malicious scripts or lifecycle hooks. This technique is highly effective against standard security audits, such as npm audit or manual reviews of the node_modules directory, as the installed package appears to be a legitimate, non-malicious version of the crypto library.
Developers investigating a breach might find running processes or suspicious network connections but find no traces of the initial infection vector in their project's dependency tree.
By March 2026, the integration of Artificial Intelligence had fundamentally transformed the speed and scale of supply chain operations, for both defenders and attackers. AI-powered reconnaissance tools now allow threat actors to scan thousands of open-source repositories and vendor policies in minutes, identifying leaked credentials or unpinned dependencies with a level of precision that was previously impossible.
One of the most concerning aspects of the Axios breach was the speed at which it cascaded through the ecosystem. Because Axios has over 100 million weekly downloads, the 11-hour window during which the malicious packages were live was enough to infect a staggering number of automated environments. AI-driven malware can now "learn" from its environment, changing its behavior to evade endpoint detection and response (EDR) tools or lying dormant when it detects a sandbox environment.
The failure of OIDC Trusted Publishing in the Axios incident has profound implications for the future of software distribution. The reliance on a "trusted" maintainer model is being re-evaluated as attackers increasingly target the human and environmental weaknesses surrounding the code rather than the code itself.
Industry experts in 2026 are advocating for a shift toward "identity-as-critical-infrastructure". This approach treats software dependencies, OAuth tokens, and machine identities as untrusted by default, requiring continuous monitoring and rapid revocation capabilities. The Axios attack demonstrated that even a cryptographically secured pipeline can be bypassed if long-lived, high-privilege tokens remain in use outside of that pipeline.
For organizations affected by the Axios supply chain attack, the priority must be on comprehensive containment and recovery. Due to the RAT's ability to exfiltrate secrets and establish persistence, a standard npm update is insufficient to guarantee safety.
Security teams should immediately audit their dependency trees for any presence of the affected versions. Because the malware uses a self-deletion protocol, teams should not rely solely on the presence of setup.js or package.json hooks as indicators of clean environments.
The Axios compromise of 2026 marks the end of an era of implicit trust in open-source registries. As organizations move forward, the focus must shift toward architectural resilience and automated validation of the software supply chain.
The integration of AI-driven security scanners, such as Socket AI, has proven to be one of the few effective defenses against this type of sophisticated malware. These tools can identify suspicious patterns—such as the dynamic loading of child_process and the exfiltration of system metadata—even when the code is heavily obfuscated. Future defense strategies will likely rely on these "autonomous defenders" to monitor dependency updates in real-time, blocking any package that deviates from established behavioral profiles.
Enterprise security teams should enforce a global --ignore-scripts policy for all automated build environments. This simple measure would have prevented the execution of the plain-crypto-js dropper in the majority of affected CI/CD pipelines. Furthermore, the use of private, vetted mirror registries for open-source packages is becoming a mandatory requirement for highly regulated industries.
The supply chain attack on Axios in March 2026 was a precisely engineered operation that targeted the core of the modern web infrastructure. By hijacking a trusted maintainer and bypassing OIDC security protocols, the attackers were able to distribute a high-impact Remote Access Trojan to millions of users. The technical sophistication of the plain-crypto-js dropper—from its multi-platform payloads to its aggressive forensic evasion—demonstrates that 2026 threat actors are operating with a level of maturity once reserved for nation-state actors.
For the security community, the Axios breach is a call to action. The reliance on manual trust and reputation-based reputation for package distribution is no longer sustainable. The future of cybersecurity lies in the adoption of identity-centric security, the enforcement of rigorous CI/CD hardening, and the integration of AI-driven behavioral analysis into the software development lifecycle. As we continue to build upon the foundations of open-source software, our defenses must evolve to protect not just the code we write, but the entire ecosystem of trust that allows it to function.
You can’t treat supply chain security as a dependency management problem anymore. This is an identity and execution problem that sits inside your CI/CD, your developer workflows, and your runtime environments.
If a single compromised package can execute code, establish persistence, and exfiltrate secrets before you even detect it, then your controls need to operate at that same speed.
That means:
This is exactly where teams start rethinking how they approach AppSec.
At we45, we work with security and engineering teams to:
You don’t need more tools. You need clarity on where you’re exposed, and how fast you can respond when something like this happens again.
Start there.
The 2026 Axios supply chain breach was a significant cybersecurity crisis that occurred on March 31, 2026, involving the distribution of a sophisticated, cross-platform Remote Access Trojan (RAT). Attackers compromised the widely used Axios HTTP client library on the npm registry and injected a malicious dependency called plain-crypto-js. This incident exploited upstream supply chain mechanisms, affecting an ecosystem where Axios is a fundamental building block with over 100 million weekly downloads.
The primary infection vector was the dependency named plain-crypto-js. Specifically, version 4.2.1 of this package introduced a heavily obfuscated setup.js dropper and a postinstall lifecycle hook in the package.json manifest. This script executed immediately upon installation, launching the infection sequence.
The attackers bypassed npm's OIDC Trusted Publishing by compromising a primary maintainer’s account, jasonsaayman. Evidence suggests they obtained a "classic" npm access token that was not constrained by OIDC. This allowed the adversary to manually publish the poisoned packages directly via the npm CLI, completely circumventing the project’s official, cryptographically-secured CI/CD pipeline.
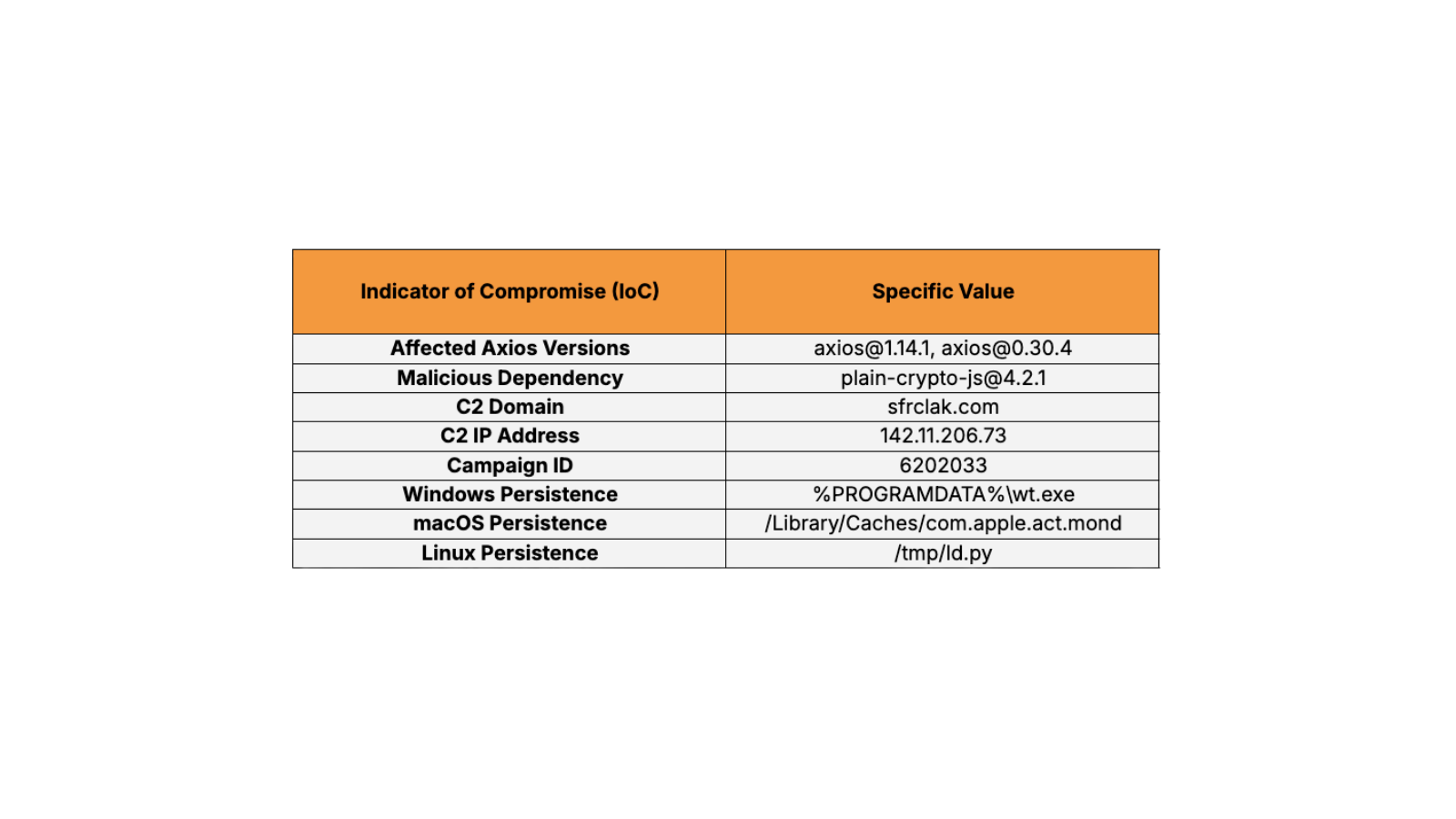
Security teams should immediately audit their environments for the affected Axios versions: axios@1.14.1 and axios@0.30.4. The primary malicious dependency is plain-crypto-js@4.2.1. Key network IoCs include the Command and Control (C2) domain sfrclak.com and the IP address 142.11.206.73, operating on port 8000. The campaign identifier used for dynamic C2 pathing was 6202033.
The second-stage RAT employed platform-specific persistence paths: Windows: The malware copied the legitimate PowerShell executable and renamed it to %PROGRAMDATA%\\wt.exe. macOS: The final persistence path was /Library/Caches/com.apple.act.mond, which is designed to mimic legitimate Apple system daemons. Linux: A Python-based RAT script was executed using nohup to detach from the parent process and was saved to /tmp/ld.py.
The RAT was configured for the large-scale exfiltration of sensitive information and secrets from infected cloud-native and server-side environments. This targeted: Cloud Provider Credentials, such as AWS access keys, GCP service account tokens, and Azure AD credentials. Deployment Secrets, including SSH private keys, npm access tokens, and GitHub personal access tokens. Environment Configuration, specifically secret keys, database passwords, and API endpoints stored in .env files. Container and Kubernetes Tokens.
Due to the RAT’s ability to establish persistence and exfiltrate secrets, a standard update is insufficient. Remediation requires five critical steps: Pin Dependencies: Downgrade Axios to a safe version (1.14.0 or 0.30.3) and explicitly pin it in package.json. Purge and Reinstall: Completely remove the node_modules directory and clear the local npm cache (npm cache clean --force). Reinstall dependencies using the --ignore-scripts flag. Hunt for Running RATs: Search for the specific persistence artifacts using system monitoring tools. Any compromised system must be rebuilt from a known-good state, not just cleaned in place. Rotate All Secrets: Immediately rotate every credential present on an infected machine, including AWS access keys, SSH private keys, and cloud provider service principals. Audit CI/CD Pipelines: Review historical build logs for installations that occurred during the window of compromise to identify leaked secrets.
Preventative strategy must shift toward architectural resilience and automated validation: Enforce Policy-Based Installation: Implement a global --ignore-scripts policy for all automated build environments. Adopt Identity-Centric Security: Treat all software dependencies, OAuth tokens, and machine identities as untrusted by default, requiring continuous monitoring and rapid revocation capabilities. Use AI Defense: Integrate AI-driven security scanners, like Socket AI, to monitor dependency updates in real-time, detecting suspicious behavioral patterns (such as dynamic loading of child_process) even if the code is obfuscated. Mirror Registries: Use private, vetted mirror registries for open-source packages in highly regulated environments.